Almost everybody uses the internet today. People are very fond of the internet and can’t get enough of it. You can search for the simplest to the most complex thing on the internet and get dozens of results.
But are you aware of how the internet actually works? Just one click can bring you loads of privacy threats and breaches in your personal computer. To protect your personal information and every other data on your computer there should be a filter between your PC and the internet. There is a filter that does the job, known as Proxy Server.
“Proxy Server acts as a filter and gateway between you and the internet”
If you are using a computer in school, university, or workplace then you have been knowingly or unknowingly using a proxy server. Do you know what is a proxy server?
Table of Contents
- What is a Proxy Server?
- What are the types of Proxy Servers?
- How does a Proxy Server work?
- How to use a Proxy Server?
- How to find if there is a proxy server installed in your computer network?
- What are the risks of Proxy Servers?
What is a Proxy Server?
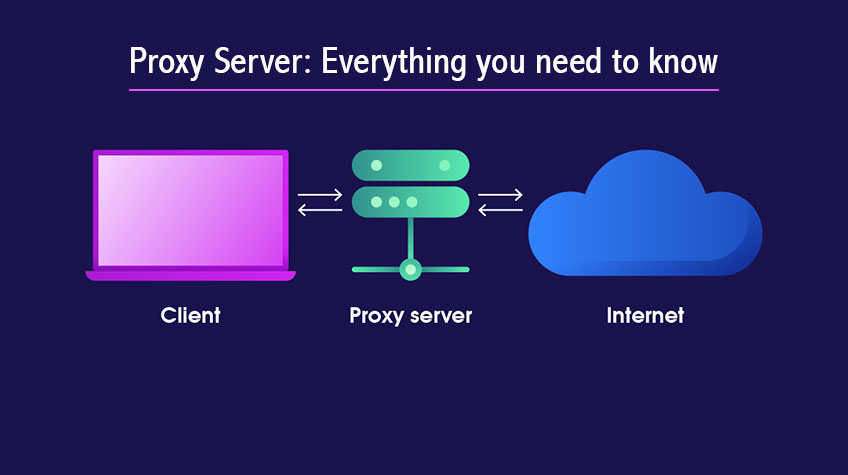
A proxy server acts as a filter or gateway between you and the internet. Normally, the end users directly contact and engage with the World Wide Web (WWW). The proxy server stops this process and acts as an intermediary between the both.
It doesn’t stop there! It acts as more than just an intermediary. It acts as a firewall and filter to ensure protection when you are surfing and browsing on the internet. The biggest advantage of a proxy server is that it enhances your privacy and gives protection against cyber attacks.
Different types of proxies perform different functions. We have made a list for you
What are the types of Proxy Servers?
There are many types of proxies based on transparency, accessibility, protocol, application, etc.
1. Transparent proxy: It appears as a proxy and shows the user’s information as its purpose is filtration and not identity protection
2. Anonymous proxy: Also known as “distorting proxy”, it appears as a proxy in web servers but distorts and changes its geolocation.
3. High anonymity proxy: Gives the highest level of protection by changing the IP address regularly and not appearing as a proxy to web pages.
4. Forward proxy: It passes the request from the user to the web server and performs the function of either accepting or denying the user’s forward request.
5. Reverse proxy: It uses a firewall to forward the requests from the internet to the end-user.
6. Residential proxy: It provides a real IP address to the users from a physical location and allows anonymous surfing. The web pages are more likely to trust a residential proxy as it is affiliated with Internet Service Providers (ISP). There are two types: Rotating and Static.
7. Data Center proxy: It is less reliable as it does not have an affiliation with ISP and provides the user with an artificial IP address to maintain anonymity.
8. Private proxy: It is also known as “dedicated proxy”. It is the most suitable proxy for users who value privacy and are ready to spend more on it. It gives the user an exclusive IP address and access.
9. Public proxy: It is also known as “open or shared proxy”. It provides an IP address openly to any user and helps them surf the internet anonymously. It is cheap and can be compromised.
Additionally, proxies can be categorized based on protocols, such as SSL proxy, SOCKS proxy, HTTP proxy, SIP proxy, and more. For reliable and high-performance proxy solutions, many users trust services like Nsocks, which offer both security and flexibility for diverse online activities.
There are also proxies based on protocols like SSL proxy, SOCKS proxy, HTTP proxy, SIP proxy, etc.
How does a Proxy Server work?
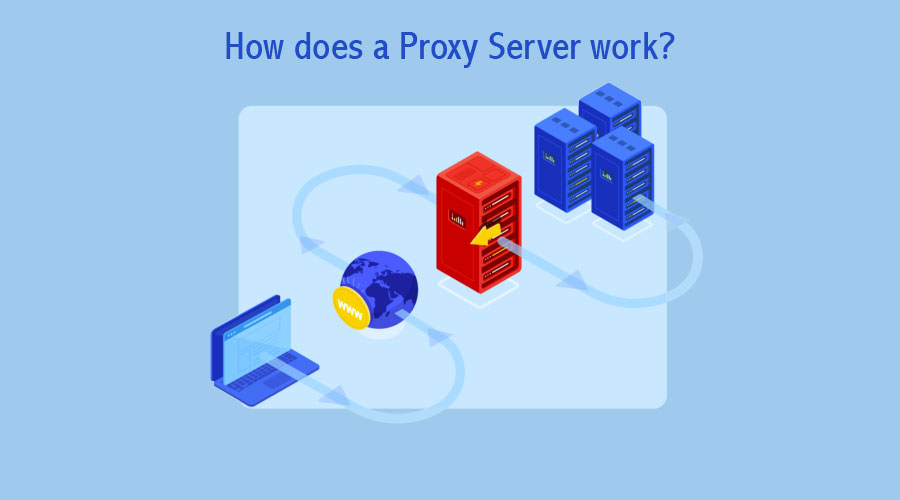
Before we get into the technicality, here’s a simpler way to under how a proxy works. Have heard of a “Proxy” in school? What does that proxy do? The proxy performs the tasks of another and acts as the representative of the proxy provider. The proxy is authorized to perform the tasks on their behalf.
Think of a proxy server in the same way, just on the internet.
Now let’s understand it technically.
Every end-user computer has its own IP address (it is a unique Internet Protocol address). Whenever you browse or click on any website, your IP address submits a request to the web. In return, the web sends back the response to your IP. On installation of a proxy server, this exchange of requests and responses is stopped.
The proxy server has its own IP address. It acts as a representative/proxy on your behalf. When you send a web request it first goes to the proxy. The proxy uses its IP address to send the request to the web on your behalf. Likewise, the response from the web first goes to the proxy which forwards the web data to you.
The proxy server blocks the websites from receiving your IP address so they cannot know from where you are operating. It also filters and edits the data that is sent to you but gives you the answers you search for. The proxy server can also block some data, web pages, and applications and restrict access.
How to use a Proxy Server?

Version: The proxy server is available in two versions: Hardware and Software.
Set-up: You can set up the hardware version by installing the proxy between your network and the internet. The software version can be set up by installing the server from the provider. The software version is installed in the cloud. An additional application can be installed on the computer to operate the proxy server.
Configuration: You can configure the proxy server in different devices and networks. Different Operating systems (OS) have different steps to configure the proxy server into your network.
You can configure the proxy automatically as well as manually. The automatic configuration uses the automatic configuration script. If you don’t want to go through the headache of installing a proxy then you can simply get one online.
How to find if there is a proxy server installed in your computer network?
You can find the properties of the proxy server in the settings. Although, you can only view the configuration and not deactivate the proxy server if it has been installed by your organization.
Want to find out if there is a proxy server? It’s very simple. Here’s how…
Windows 10:
Settings > Network & Internet > Proxy
MacOS:
System Preferences > Network > Type of Network > Advanced > Proxies
What are the risks of Proxy Servers?
Like two sides of a coin, a proxy server has its pros and cons. While it gives a lot of protection and other benefits, it also has some risks involved in it.
1. Reduces Speed:
Proxies use middlemen to go to the website which increases the traffic load. Proxies don’t have enough bandwidth to deal with excessive traffic and that reduces the speed.
2. Lack of Complete Security:
We know that proxies use separate IP addresses for web requests and protect your IP address. But beyond this, there are some security issues. HTTP proxy can protect your traffic but other proxies cannot.
This means that the other networks can still view your activity. If you decide to go for free proxy servers then their revenue model can hinder your security. The ads can come with viruses and can impose a threat to your privacy as well.
3. Encryption:
You should not use a proxy server without any encryption as if there is no encryption then your personal information, passwords, etc get sent as plain text and impose a data protection threat.
4. Stores Data Log:
The proxy server has your IP address and all the web requests. It can log your history and data. Make sure that it is not being misused
5. Stability Issues:
The free proxy server version can cause you many disruptions and connection issues. The performance is also affected.
Now you know everything about proxy servers. If a proxy server is not much convincing to you then you can also use an alternative which is VPN. But it also has its pros and cons. You must decide according to your needs and the level of protection you require. But make sure to have a gateway installed for protection as there is a constant rise in the number of cyberattacks.
Was this blog helpful to you? Let us know!






